Cloud Security Posture Management (CSPM) refers to the process of continuously monitoring and assessing the security posture of an organization’s cloud infrastructure. CSPM tools provide visibility into the security configurations and compliance of cloud applications, helping organizations identify vulnerabilities, enforce security policies, and ensure adherence to best practices.
Key Features of CSPM
Configuration Assessment
CSPM tools analyze the security cloud configurations of various cloud resources, such as virtual machines, storage accounts, databases, containers, and networks. They check for misconfigurations, non-compliant settings, and security gaps that could expose the infrastructure to potential threats.
Security Best Practices
CSPM solutions provide organizations with pre-defined security best practices and industry standards. They evaluate cloud configurations against these benchmarks and offer recommendations for remediation, ensuring that resources are configured securely.
Continuous Monitoring
CSPM tools offer real-time monitoring capabilities, enabling organizations to identify security issues as they arise. They provide alerts and notifications for misconfigurations, unauthorized access, or suspicious activities, helping organizations respond promptly to potential threats.
Compliance Monitoring
CSPM solutions assist organizations in meeting regulatory compliance requirements. They evaluate cloud environments against industry-specific standards and regulations, such as HIPAA or GDPR, and provide visibility into compliance status, making it easier to enforce necessary controls and maintain audit readiness.
Remediation and Automation
CSPM tools offer automated remediation capabilities, allowing organizations to fix misconfigurations or non-compliant settings automatically. By automating the remediation process, CSPM reduces the time and effort required to address security issues promptly.
Why CSPM is Essential for Cloud Security
Risk Mitigation
CSPM tools help organizations identify and address security risks in cloud infrastructure. By continuously monitoring configurations, organizations can proactively detect and remediate exposure, minimizing the likelihood of security breaches and data leaks.
Enhanced Visibility
CSPM provides a comprehensive view of an organization’s cloud environment. It allows businesses to identify and assess security gaps across various resources, ensuring that all components of the cloud infrastructure are adequately protected.
Compliance Assurance
CSPM solutions play a crucial role in maintaining compliance with industry regulations and standards. By continuously monitoring configurations and providing insights into compliance status, organizations can address potential compliance issues before they become problematic.
Cost Optimization
Misconfigurations in the cloud environment can lead to security breaches and financial losses. CSPM tools help organizations optimize their cloud usage by identifying unnecessary or unused resources, eliminating wasteful spending, and enhancing overall cost-efficiency.
Collaboration and Governance
CSPM solutions facilitate collaboration between IT and security teams. They provide a centralized platform for managing security policies, tracking remediation efforts, and generating compliance reports, enabling effective governance of cloud security measures.
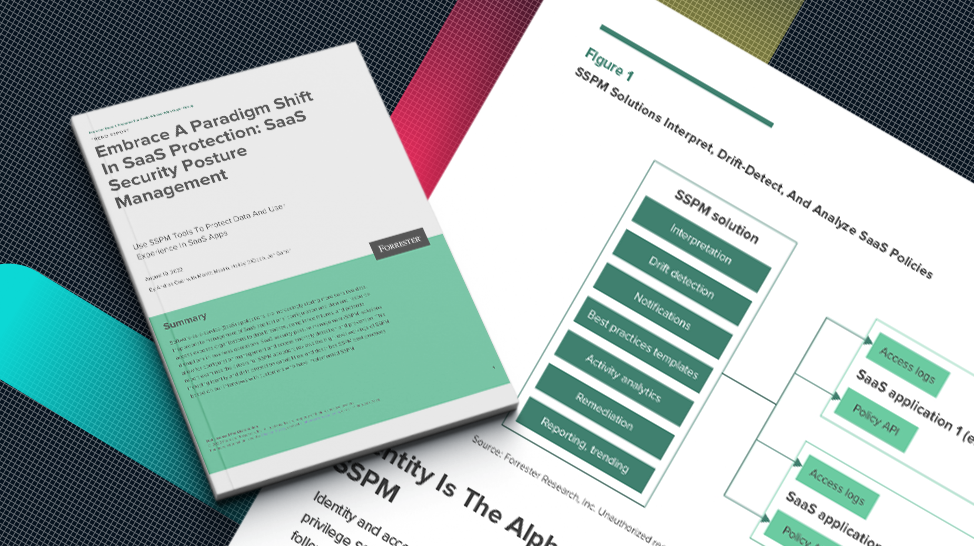
CSPM vs. SSPM
CSPMs and SSPMs do similar jobs on different areas of the cloud. SSPMs help organizations secure their SaaS applications, while CSPMs are used to secure cloud infrastructure. While their names are similar, they are not interchangeable. A CSPM is unable to secure SaaS applications, and SSPMs are unable to secure cloud infrastructure.
Together, SSPMs and CSPMs work to safeguard data by offering visibility and implementing remedial measures to address vulnerabilities to minimize risks and enhance security.