Let’s Get Technical
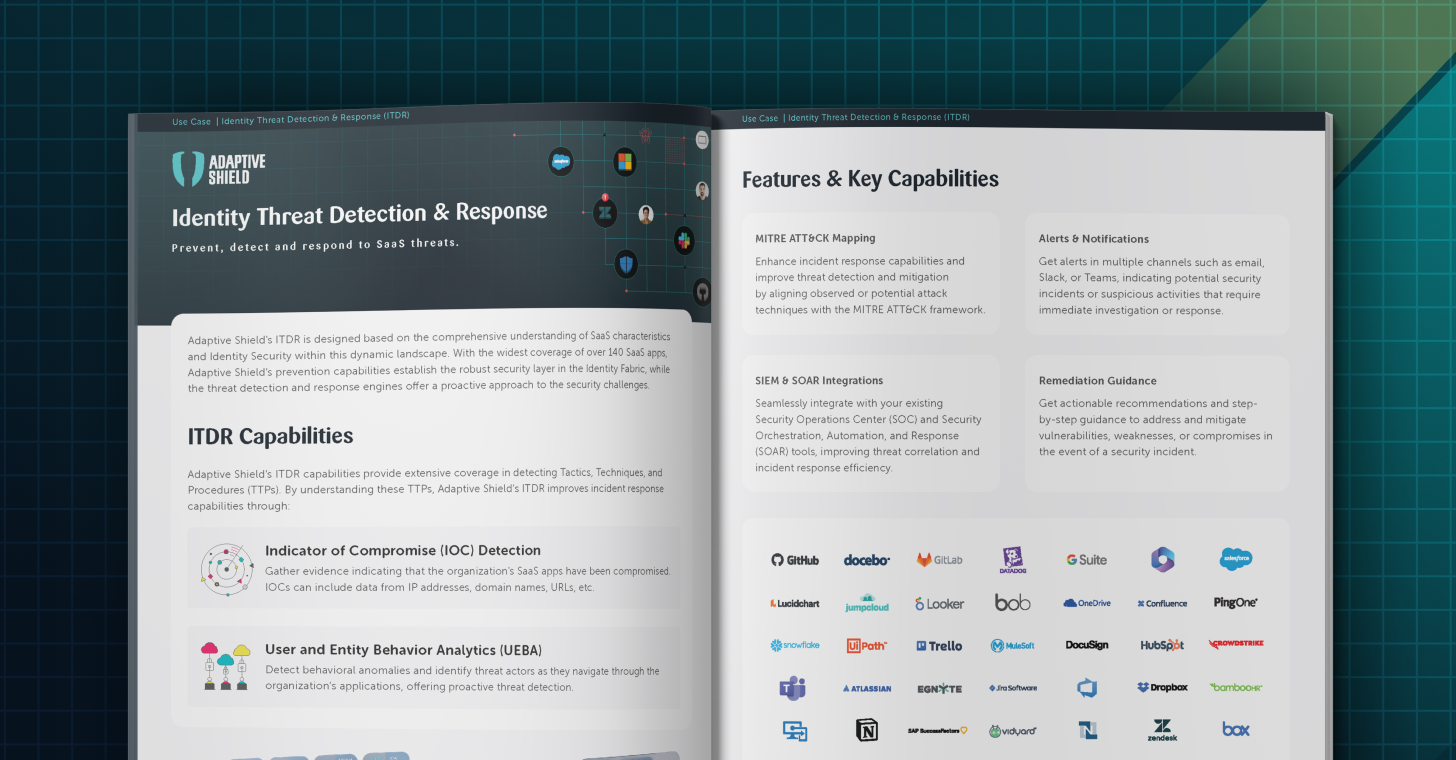
Adaptive Shield’s Identity Threat Detection and Response (ITDR) capabilities feature a set of security measures designed to detect and respond to identity-related security threats based on key Indicators of Compromise (IOCs). The platform’s threat detection engines cross-reference and analyze in-context Unusual Entity & User Behavior (UEBA) from multiple sources, enabling the accurate detection of very complex and subtle threats. Each threat in the Threat Center includes the context of the event, a recommended investigative approach, contacts who require notification, and mitigation steps.
From Threat Prevention to Protection
As a means of prevention, SSPM operates as the security layer in the Identity Fabric to establish robust user governance. As a second layer of threat protection, ITDR provides extensive coverage in detecting SaaS-related threats, such as password-based attacks, IP behavior anomalies, OAuth-based attacks, unauthorized document access, unusual user agent activities, and more.