Identity Security Posture Management (ISPM) is the practice of securing an organization’s digital identities to prevent bad actors from accessing enterprise SaaS applications to carry out identity-related threats.
Every user identity is a potential entrance into a SaaS application. These include human user accounts with roles and permissions, as well as non-human accounts for third-party integrations, such as service accounts, API keys, and OAuth authorizations. Managing the security and visibility of employees, customer accounts, partner accounts, external vendors, and other stakeholders falls under the umbrella of ISPM.
Strengthening an organization’s identity fabric through ISPM ensures that these identities are protected, appropriately managed, and in accordance with company policy. The following elements enable a strong ISPM program.
Identity Governance
Identity governance is a framework that establishes policies and processes for the creation, modification, and deletion of digital identities. In SaaS, identity governance is essential for ensuring the security, compliance, and integrity of user identities and access privileges within cloud-based software applications and services. It helps organizations effectively manage and govern user access while minimizing security risks and maintaining regulatory compliance.
Access Control and Authentication
SaaS applications are designed to be accessed from anywhere at any time. While this provides flexibility and convenience, it introduces significant risks if left unmanaged. SaaS security demands strict access control measures to ensure that authorized users can only access the data and services needed to perform their job functions.
Strong access controls and authentication methods, such as multi-factor authentication (MFA) and Single Sign-On (SSO), verify the identity of users attempting to access the system.
Authorization and Permissions
Organizations define roles for users and systems based on their responsibilities and functions. These roles often correspond to specific job titles or functional areas within the organization.
By tracking each user’s roles on applications, the security team can identify all users with advanced permission sets, such as admins.
Enforcing the principle of least privilege (POLP) across the organization ensures that users have access to the resources they need to perform their jobs without unnecessarily expanding the attack surface.
User Discovery
User discovery is the process of identifying all users with access to SaaS applications. In addition to gaining in-depth knowledge of user permissions and behavior, security teams can find users who are overprivileged, dormant, external, or partially deprovisioned. Identifying these users and removing or adjusting their access permissions is a key component of ISPM.
User Monitoring
User monitoring tracks user behaviors within each application. This enables identity threat detection and response tools to recognize anomalous behavior in the event an account is compromised.
Monitoring for Identity Security Posture Management includes identifying the location, device, operating system, and browser typically used by a user. Additionally, it tracks typical user behaviors, both as an individual and as a role. Unexpected behaviors constitute indicators of compromise, and often merit an investigation.
User Consolidation
Different usernames are often used by a single user in different applications. Consolidating all those names within one account enables more accurate user management and tracking. For example, an admin may have access to an account through the company’s SSO, and local access through an email address, which may be different from the identity used for SSO. That single user’s multiple names should be tracked as a single user.
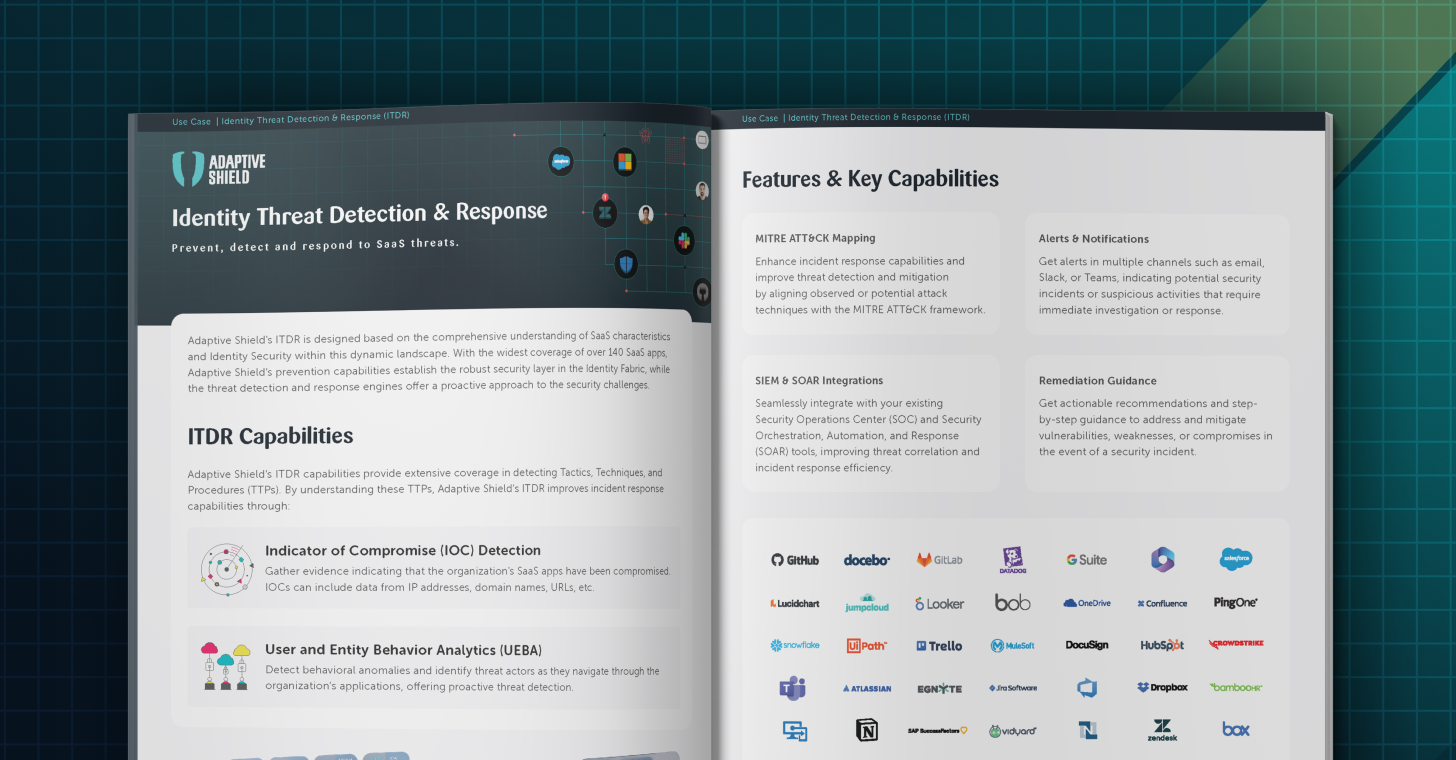
Identify and defend against threats with ITDR
Having multiple identity security layers increases an organization’s ability to protect itself from breaches. Identity threat detection and response (ITDR) solutions detect when an identity has been compromised, and allow the security team to address the event.
Key ISPM Capabilities
To be effective, an Identity Security Posture Management solution should have visibility into a number of different types of users.
Active users
Requires visibility into the apps the user is authorized to access, and the role the user has. Additionally, it should provide visibility into any high-privileged roles assigned to the user, and list all groups that the user is assigned to.
Dormant users
Shows users who have been inactive for a predetermined time period from the entire SaaS stack or just an individual application. Dormant user accounts are at risk of being breached without anyone noticing. In addition, they may have associated licensing fees.
External users
Organizations must be able to monitor external users, and track their activities to ensure that they are not acting against the company’s best interests.
Unmanaged users
Oftentimes these users are former employees who have been removed from the organization’s identity provider (IdP) but have retained local access that doesn’t require MFA or SSO.
Non-human users
These accounts must be monitored, as they frequently have high privileges and don’t require any secondary authentication. They pose a significant security risk if taken over by threat actors.
ISPM is a Key Piece of SaaS Security
Identity Security Posture Management is essential for protecting an organization’s SaaS applications. It ensures that only authorized users can access sensitive information, and addresses one of the most critical attack vectors – user identities. Once a SaaS application is compromised, identity information can be taken by threat actors for a range of common attacks including phishing, ransomware, and malware.
A strong Identity Security Posture helps protect SaaS applications against data breaches, insider threats, and third-party access risks.